KNOWLEDGE CENTER
What is a Security Vulnerability?
A Security vulnerability refers to any weakness capable of being exploited by a bad actor. According to ISO 27002, a vulnerability is “a weakness of an asset or group of assets that can be exploited by one or more threats.”
Threats are any situation or tactic that can exploit a vulnerability to cause damage to an asset. In security we typically measure in “risk” and our goal is to understand, mitigate, and control that risk. In this sense, risk is the marrying of threats and vulnerabilities.
An exploit refers to the manner in which the vulnerability is exposed, usually through a code or tool. Depending on the vulnerability exploited, the impact can be disastrous, compromising your data and granting cyber attackers free run of your company’s systems, code, and otherwise sensitive data.
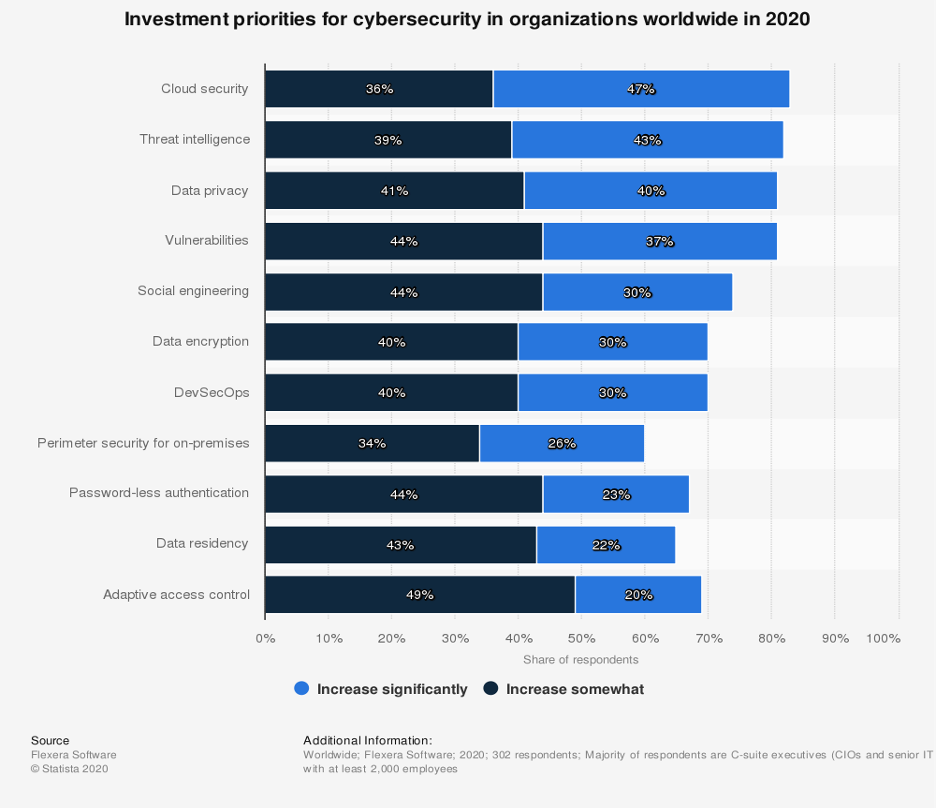
Due to the prevalence of cyber threats, many companies have begun to re-assess their priorities. Vulnerabilities now only come behind cloud security, threat intelligence and data privacy when it comes to cyber security investment priorities.
Vulnerabilities can be leveraged to force software to act in ways it was not intended to, such as assembling information about the current security defenses in place at an organization. Vulnerabilities become exposed to cyber threats for a number of reasons. Often, the product type can be at issue. Several operating systems contain a high level of vulnerabilities, including Debian Linux, Android and Linux Kernel.
What’s more, the rise of the Internet of Things has fostered a playground of cyber attacks. After all, how often does one consider their printer to be vulnerable to cyber threats?
Common Types of Security Vulnerabilities
To manipulate a vulnerability, the bad actor has a number of exploits at their disposal. Some common examples include:
SQL Injection
SQL injection is among the most common of vulnerability exploits. It’s accomplished by “injecting” a malicious payload (which could potentially wreck your data) within a web page or application. Once injected, the attacker can make malicious SQL commands directly in your database, allowing them to access and steal the credentials of users within a system.
Broken Authentication
When authentication credentials are stolen or compromised, system access and user identities can be appropriated by malicious actors to pose as the intended user, gaining access to critical systems and information.
Cross-Site Scripting (XSS)
Another injection-style attack, an XSS attack targets web browsers in an attempt to use malicious scripts to steal or destroy information. However, an XSS attack targets individual users rather than the organization itself. To do this, malicious code is embedded into an otherwise-legitimate web page or app (usually a forum or message board). When a user visits this page, the malicious script is sent to the user’s browser. With JavaScript, cross-site scripting allows bad actors access to a user’s cookies. This puts the user’s identity at risk and, in HTML5, can also compromise their geolocation, webcam and microphone.
Security Misconfiguration
Security misconfiguration is the lack of proper security in server or web apps, opening up your business to cyber threats. This kind of misconfiguration runs rampant, commonly occurring when levels of the application stack are upgraded while others are left untouched, as the default settings may have included insecurities that go unaddressed.
Exploited Security Vulnerabilities
Due to the novel coronavirus pandemic, cyber threats have picked up significant steam. Schools and businesses turned to software company Zoom as they shifted their resources online. It wasn’t long before Zoom’s many vulnerabilities were exploited by cyberattackers, putting the company at severe risk during a time of high growth.
And more U.S. companies have been targeted. In the first quarter of 2020, 8.4 billion records were leaked — compare that with the 4.1 billion leaks due to cyber threats in 2019’s first half.
With more businesses extending their remote workforces indefinitely, a petri dish of vulnerabilities remain, waiting to be exploited. Which vulnerabilities might your company be facing?