ENTERPRISE VULNERABILITY MANAGEMENT
“The time savings we see with Nucleus are unreal”
– Security Analyst
Accelerate Vulnerability Response
Nucleus is built to solve the tedious vulnerability management process through data unification and smart automation of tasks throughout the entire workflow. Sitting at the nexus of your vulnerability data, asset information, and embedded threat intelligence – Nucleus provides contextually relevant data at your fingertips, allowing for automated response at scale.
CENTRALIZED
INFORMATION.
Use Nucleus to manage and monitor all vulnerabilities discovered via scanning, penetration testing, or compliance audits – in one location.
CUSTOMIZED
PRIORITIZATION.
Customize the Nucleus risk-scoring algorithm to ensure vulnerabilities are correctly prioritized, alongside integrated threat intelligence.

AUTOMATED
REMEDIATION.
Fix vulnerabilities faster and with less resources using automation rules to trigger alerts, create tickets, send reports, and more.
All-in-One Data Aggregation & Process Automation Software
Nucleus unifies existing tools in your security stack, creating a centralized hub to control the chaos of vulnerability analysis, triage, and remediation.
CENTRALIZED VULNERABILITY INFORMATION
Vulnerability scanning and discovery is just the first step towards an enterprise vulnerability management program. Nucleus ingests and normalizes all of the vulnerability data in your enterprise, enabling your organization to:
- Analyze, track and search all vulnerability information, from all tools, penetration tests and audits, from a single console
- Organize your assets and corresponding vulnerability data to best fit your monitoring and reporting requirements
- Automate your vulnerability management workflows and triage processes
- Maintain accountability and measure key performance indicators for each business unit, department or subnet
SEE IT IN ACTION >
CUSTOMIZED VULNERABILITY & RISK PRIORITIZATION
Every organization has a different approach and methodology to prioritizing vulnerabilities. Nucleus lets organizations customize the vulnerability prioritization and risk scoring algorithm based on the vulnerability attributes that are most important to the vulnerability management team, alongside integrated threat intelligence from Mandiant. Resulting in:
- Continuous vulnerability and asset risk scoring that is contextual to your organization
- Massive reduction in time spent determining the risk of each vulnerability based on the assets affected
- Accurate risk reports based on vulnerability intelligence, threat intelligence, and asset context
START A FREE TRIAL >
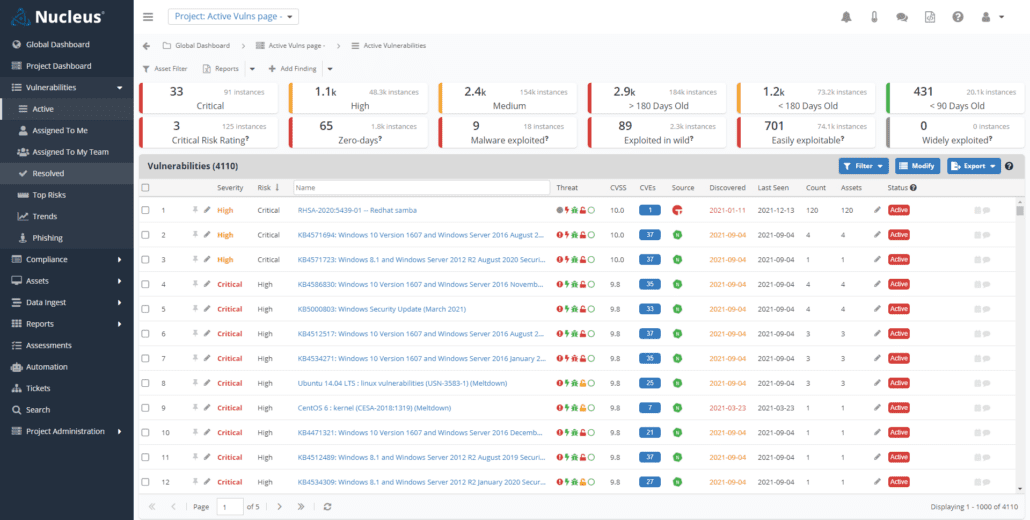
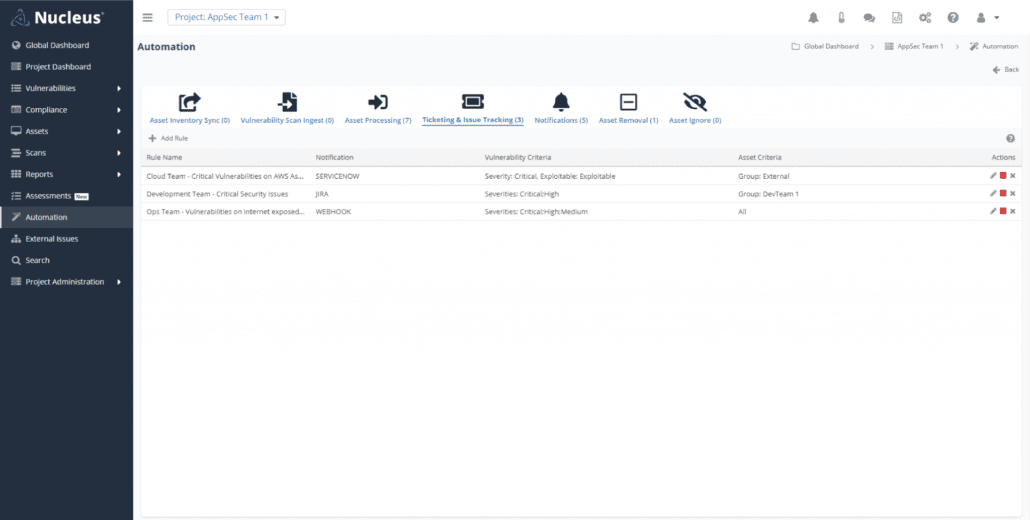
AUTOMATED REMEDIATION WORKFLOWS
The most time-consuming phase of vulnerability management is the remediation process. Each vulnerability must be assigned the correct team or individual for remediation, tracked, and confirmed to be fixed once remediation occurs. Nucleus automates this process, saving you time and greatly improving your time to remediate through:
- Bi-directional integrations with ticketing systems, issue trackers, incident response tools, SIEMs and more
- Flexible automation rules to automate your existing vulnerability management workflows and processes
- Real-time views of all active vulnerabilities and their current remediation status
BOOK A DEMO >
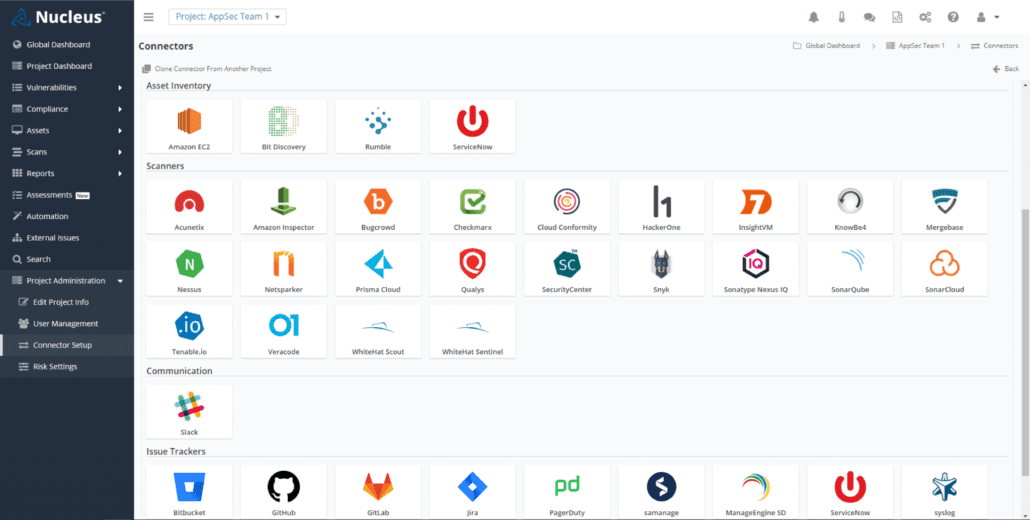
Unlock the Value of Your Existing Tools
Integrating with over 100 scanners and external security tools, Nucleus ingests the entire scope of vulnerability data available to your enterprise and consolidates it into one place, automating the remediation process so teams work more effectively.
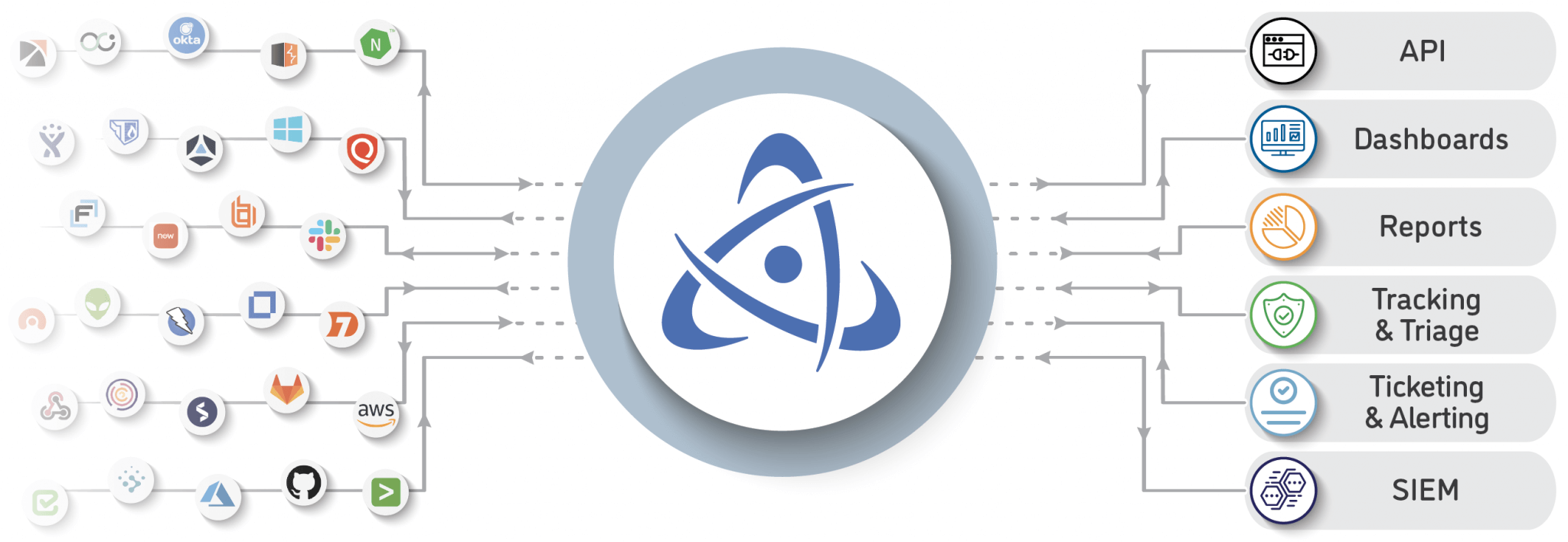
100+ Integrations
Speed & Scalability
SSO & Custom Roles
Risk Reporting
Integrated Threat Intelligence
Pen Test & Audit Results
NUCLEUS RESOURCES
Fixing the Broken Vulnerability Management Process
Broken VM processes continue to plague organizations large and small. As the vulnerability landscape continues to evolve rapidly, the processes used to discover, track, and remediate them has failed to evolve with it. In this eBook, we explore the importance of maintaining a contemporary VM program and the critical components used to build one.
Start Remediating Vulnerabilities 10x Faster. Start Your Free Trial Today!