NUCLEUS BLOG.
How Nucleus Security Streamlines Vulnerability Management for Government Agencies
How Nucleus Security Streamlines Vulnerability Management for Government Agencies Nucleus Security is proud to announce its recent achievement of Federal Risk and Authorization Management Program
5 Things to Consider Before Using SSVC to Automate Vulnerability Prioritization
5 Things to Consider Before Using SSVC Vulnerability Prioritization Framework Vulnerability prioritization is one of the most important steps in managing cybersecurity risks effectively. Ideally,

National Cyber Security Centre (NCSC) Vulnerability Management Guidance 2.0 Checklist
National Cyber Security Centre (NCSC) Vulnerability Management Guidance Checklist As of February 12, 2024, the National Cyber Security Centre (NCSC) has released Version 2.0 of

How Nucleus Security’s $43M Series B Funding Powers Enterprise Risk-Based Vulnerability Management Innovation
How Nucleus Security’s $43M Series B Funding Powers Enterprise Risk-Based Vulnerability Management Innovation We at Nucleus Security are thrilled to share our journey and vision
Nucleus Product Update 4.1
Multiple connector additions and new in-platform customizations Welcome to the Nucleus Product Update 4.1. It’s a new year with new things to get excited about

6 Behaviors That Hinder Vulnerability Management Maturity
6 Behaviors that Hinder Vulnerability Management Maturity I’ll be honest – the last time someone asked me to assess my behavior was in therapy. Difficult?
Release Spotlight: Orca Connector
Release Spotlight: Orca Connector Imagine navigating the vast, unpredictable ocean, where every wave and current brings a new challenge. This turbulent navigation experience mirrors the

How to Adapt Vulnerability Management Service Level Agreements (SLAs) to Team Maturity
How to Adapt Vulnerability Management Service Level Agreements (SLAs) to Team Maturity In working with customers across different enterprises and experiencing it myself, the challenges
Release Spotlight: Qualys PCS
Release Spotlight: Qualys PCS In the culinary world, the adage “too many cooks spoil the broth” warns of the chaos and disarray that can arise
Nucleus Product Update 3.9
Platform Upgrades, Lacework, Findings Processing Re-Ordering, and more! Welcome to the Nucleus Product Update 3.9. As we approach Thanksgiving, we’d like to start by expressing

NYDFS Regulatory Changes: Vulnerability Management and Risk Assessment
NYDFS Regulatory Changes: Vulnerability Management and Risk Assessment The financial sector is constantly adapting to emerging threats and regulatory changes. The New York Department of
Release Spotlight: Lacework Connector
Release Spotlight: Lacework Connector Navigating a city without a map or GPS can lead to unexpected dead-ends or hazardous zones. Similarly, managing your cloud infrastructure
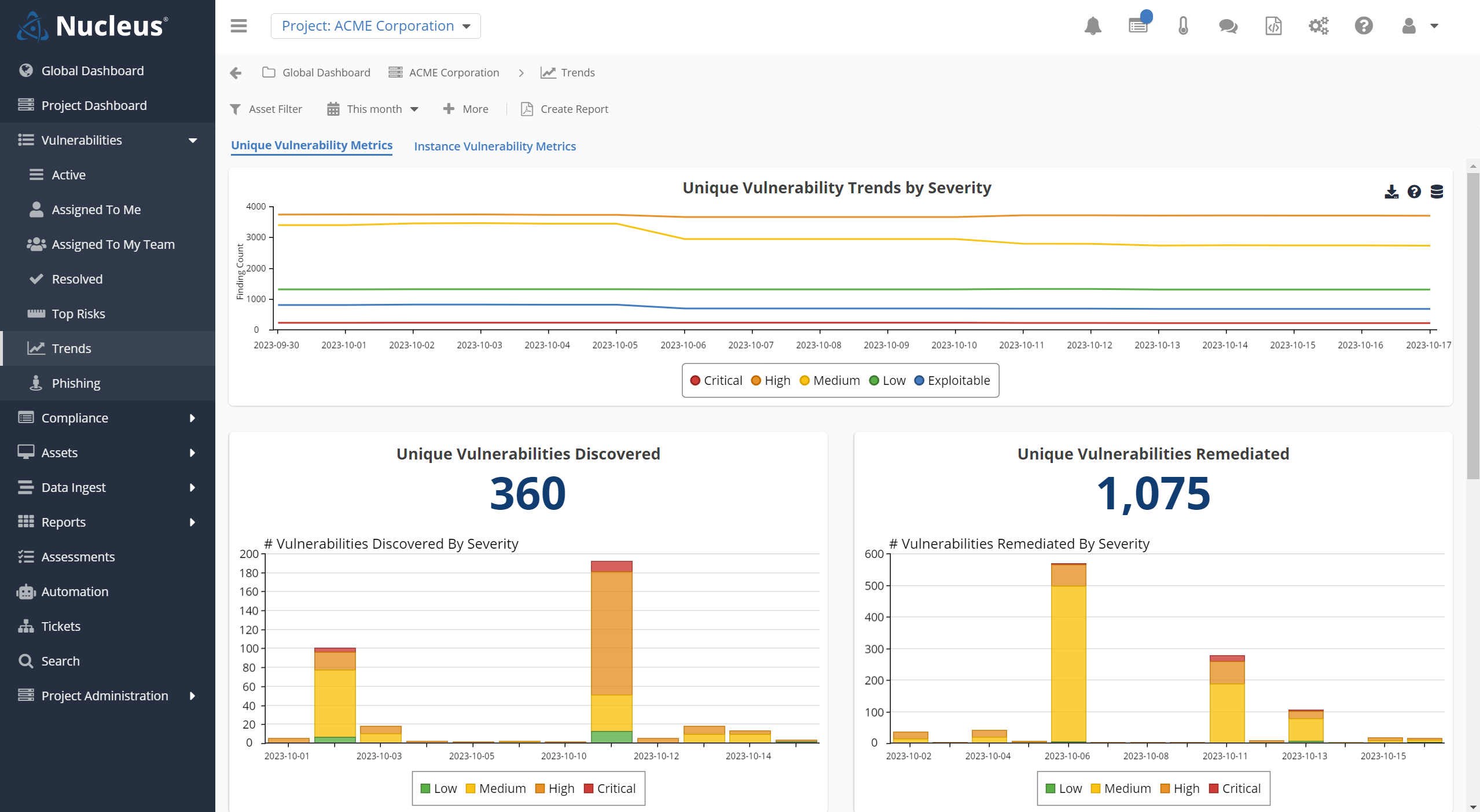
Release Spotlight: Trends Page Upgrade and Bulk Data Export Functionality
Release Spotlight: Trends Page Upgrade and Bulk Data Export Functionality In vulnerability management (VM), the task of sifting through vast amounts of data to pinpoint
CISA KEV Ransomware Interactive Visualization
Looking at CISA KEV Associated with Ransomware When we first built the CISA KEV enrichment dashboard at Nucleus, our goal was to gain new insights
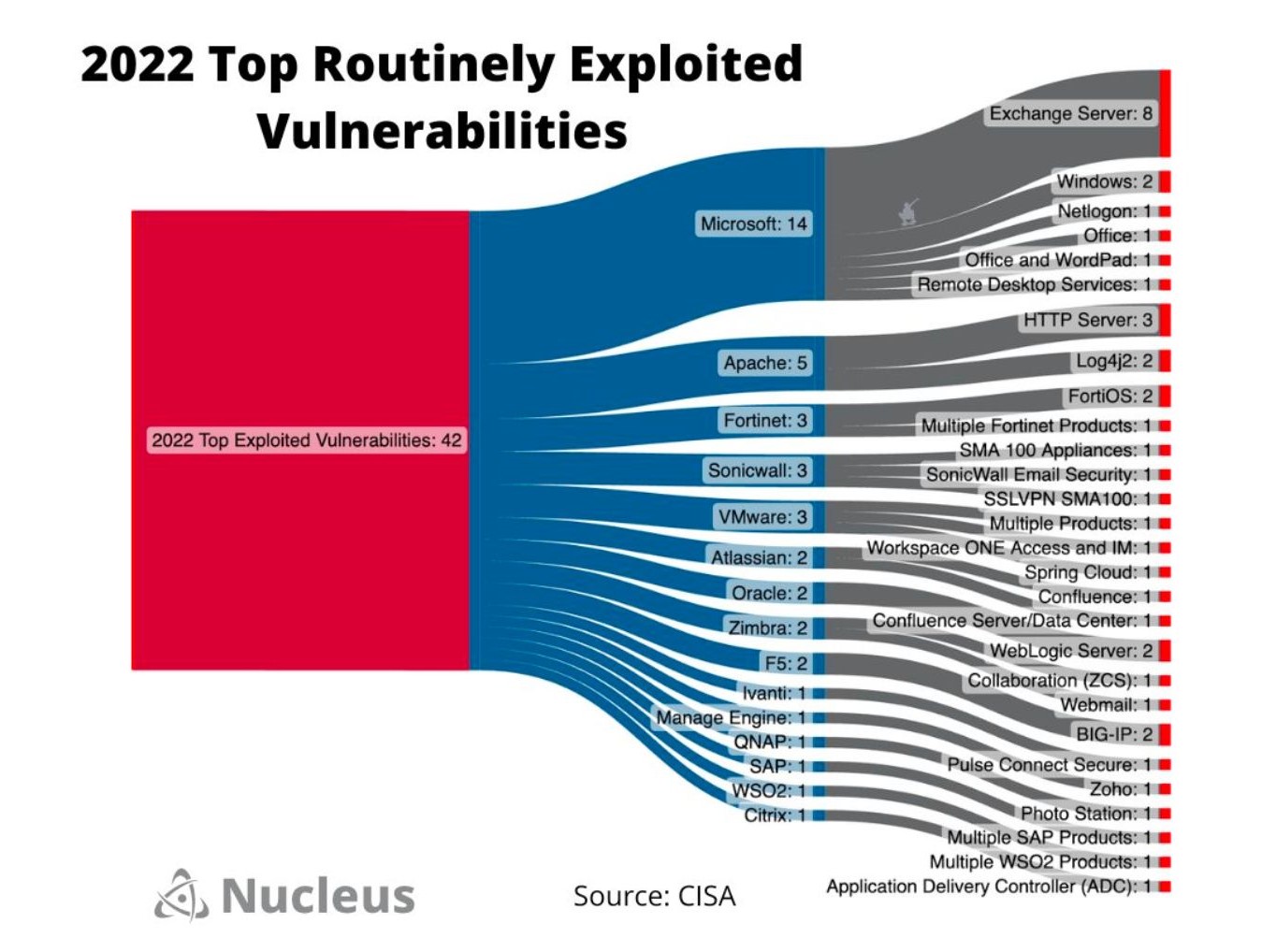
A Look at CISA’s Top Routinely Exploited Vulnerabilities
A Look at CISA’s Top Routinely Exploited Vulnerabilities Knowing what vulnerabilities interest malicious actors is a critical step in assessing the risk of vulnerabilities found